Lattice troubleshooting guide
Troubleshoot common issues and errors with Amazon VPC Lattice
Cloud Dedicated is currently in invite-only preview. Don't hesitate to get in touch if you'd like to request access or have any questions or feedback.
Refer to the configuration page to learn how to configure AWS VPC Lattice to send traffic to your subgraphs.
Enable subgraph error inclusion
To help resolve AWS VPC Lattice connection issues, enable subgraph error inclusions for your graph variant. This configuration lets you see error messages generated by your subgraphs. Follow these steps to set the configuration:
- Go to GraphOS Studio.
- Open the Cloud Router page from the left navigation.
- Open the Configuration tab.
- In Router configuration YAML, ensure your configuration has the following configuration block:
include_subgraph_errors:all: true
- Click the Save button in the top right corner of that section.
Configuration changes trigger a new launch. Please wait a few minutes for your cloud router to update with this new configuration. You can track your graph variant's deployment status on its Launches page.
Once you've found and resolved the issue, Apollo recommends turning off subgraph error inclusion. To do so, remove the include_subgraph_errors configuration. Then, save the router's configuration YAML.
Common issues and errors
If you encounter an error not listed below and need help, don't hesitate to get in touch with your Apollo contact. We're here to help.
Overriding host headers
Amazon VPC Lattice relies on the host header to secure and route requests. You can't change this header on Cloud Dedicated. Instead, consider using a header like x-host. You can rewrite an incoming header through your router configuration YAML:
# ...other configuration...headers:all: # Header rules for all subgraphsrequest:- propagate:named: 'host'rename: 'x-host'
The previous example renames a host header to x-host.
Service in resource share doesn't appear in private subgraphs
Cloud Dedicated doesn't automatically scan your resource shares for new Lattice services. If you add a service, you can manually trigger a scan by going to your Apollo Organization settings page and clicking the Rescan subgraphs button.
Providing Authorization headers
Because AWS Sigv4 relies on the HTTP Authorization request header for signing requests, you may receive an error like this: You must be authenticated to access this resource. Please provide a valid Bearer Token in the Authorization header.
If your subgraphs rely on the Authorization header for authentication, your router must rename it. For example:
# ...other configuration...headers:all: # Header rules for all subgraphsrequest:- propagate:named: 'Authorization'rename: 'X-Authorization'
Then, update your subgraphs to check for Authorization or your new header name.
Error trying to connect: Connection reset by peer (os error 104)
This error is likely to occur when your cloud router tries to send traffic to a port different from the listener on your AWS VPC Lattice service. Apollo GraphOS Cloud only supports communicating with private subgraphs over HTTPS on port 443.
You can check that a Lattice service is configured to receive traffic on the right port on a service's Routing page:
- In the AWS Console for your region of choice, go to the VPC service page.
- In the left navigation, scroll down and open VPC Lattice > Services.
- Click the Lattice service used by the subgraph in question.
- Click the Routing tab.
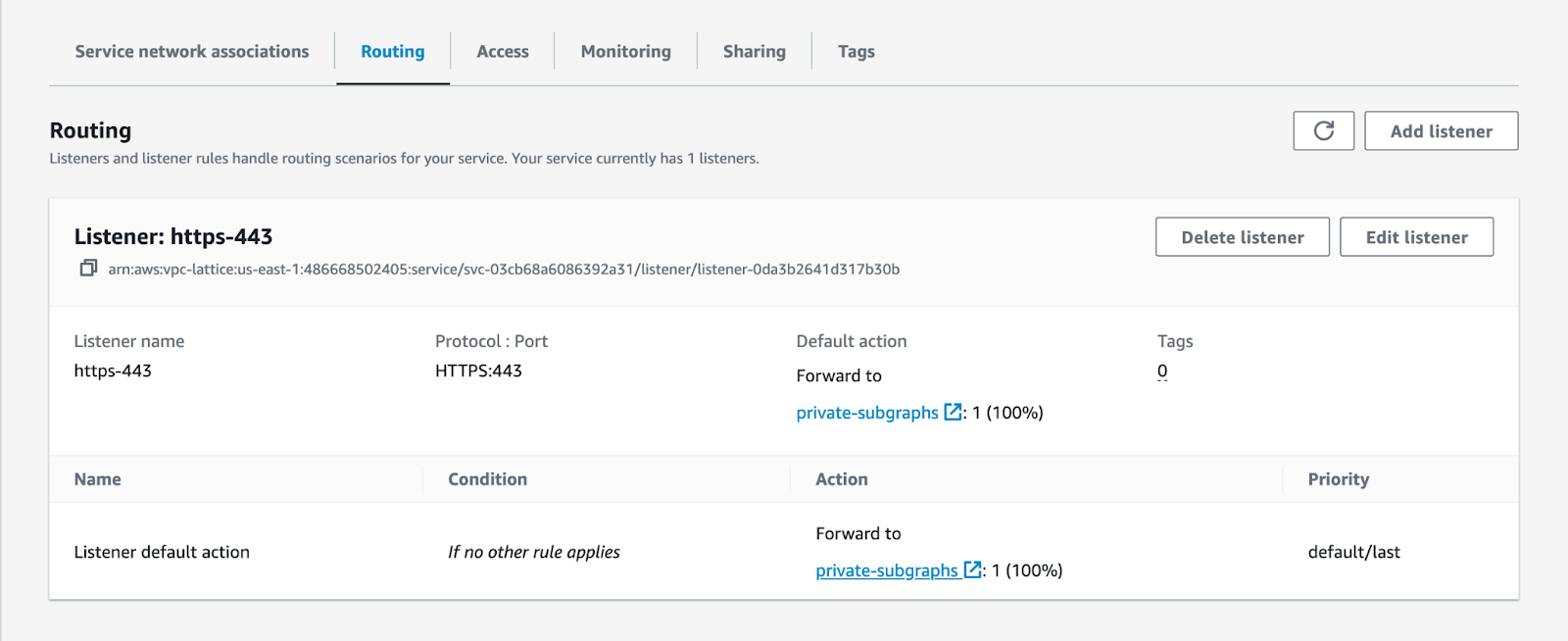
- Check that you have a listener with a
protocol:portconfiguration of HTTPS:443.
If not, you must create a new listener by clicking on the Add listener button at the top left of this section. Refer to step 10 of Create a Lattice service for more details.
HTTP fetch failed from '_subgraph_': 403: Forbidden
This error likely occurs for one of the following reasons:
- One of your clients is sending a subscription request to a private subgraph over WebSockets.
- The VPC Lattice IAM policy doesn't allow traffic from Apollo GraphOS Cloud.
Subscriptions over WebSockets
Subscriptions over WebSockets aren't supported in AWS VPC Lattice, as the platform currently lacks WebSocket support. When sending a request to upgrade to a WebSockets connection, Lattice returns a blank response with a 403 response code. In this situation, Lattice also doesn't emit access log entries to Amazon CloudWatch Logs. Contact your AWS account team to notify them of your interest in this feature.
VPC Lattice IAM policy
You can check that a Lattice service is configured to allow traffic from Apollo GraphOS Cloud on the service's Access page:
- In the AWS Console for your region of choice, go to the VPC service page.
- In the left navigation, scroll down and open VPC Lattice > Services.
- Click the Lattice service used by the subgraph in question.
- Click the Access tab.
- Ensure that the Auth type is set to IAM and that the policy looks like this:
{"Version": "2012-10-17","Statement": [{"Effect": "Allow","Principal": "*","Action": "vpc-lattice-svcs:Invoke","Resource": "*","Condition": {"ForAnyValue:StringLike": {"aws:PrincipalOrgPaths": "o-9vaxczew6u/*/ou-leyb-l9pccq2t/ou-leyb-fvqz35yo/*"}}}]}